The Justice Department has issued arrest warrants for two Syrians who are accused of hacking the Marine Corps' recruiting website in September 2013.
Ahmad Umar Agha, 22, and Firas Dardar, 27, allegedly used a spear-phishing attack to obtain password information from an advertising company employee that allowed them to take control the Marines.com website, according to the criminal complaint against the two.
For roughly six hours, Marines.com redirected users to a website that urged Marines to "refuse your orders" and fight with Syrian forces under the control of President Bashar al-Assad, the complaint says. Neither of the alleged hackers is in U.S. custody.
While the investigation into the hacking is a triumph for law enforcement, the victory may be a symbolic one only, said Bryan Gorczyk, a cybersecurity expert and former FBI agent.
"These cases are extremely important to do," Gorczyk told Marine Corps Times. "We just can't let people run roughshod over our websites and our infrastructure. Unfortunately, in this case, I don't know the odds of being to able to legally get these people out of the country, get them to actually stand charges. I expect it's going to be very, very low."
Gorczyk said he does not foresee Syria handing over the two alleged hackers to U.S. authorities, so the best chance law enforcement has to nab them would be if they go to a third country with which the U.S. has an extradition treaty.
"The charges will stand forever until they're caught," he said. "I think the takeaway is we did something incredibly important, incredibly sophisticated in terms of the investigation ... but unfortunately, I don't know that we're ever going to see these [suspects] in a court hearing in the United States."
The FBI has placed both Agha and Dardar on its Cyber Most Wanted list, said Justice Department spokesman Peter Carr.
"As with any charged by the United States, the department will seek to bring them to justice here in the United States," Carr said in an email to Marine Corps Times.
At the time of the attack, a Marine Corps spokesman stressed that Marines.com does not contain any sensitive or personally identifiable information and now .mil websites with a .mil suffix were breached in the attack.
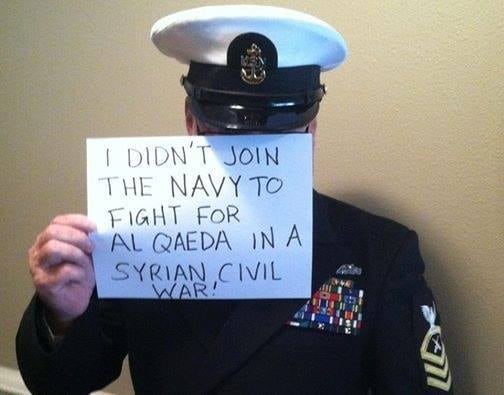
Syrian hackers took over the Marine Corps' recruiting website in September 2013.
Photo Credit: Facebook image
The government said Agha, known online as "Th3 Pr0," and Dardar, known as "The Shadow," are members of the special operations division of the Syrian Electronic Army, a group of hackers responsible for computer intrusions intended to punish perceived detractors of Syrian President Bashar al-Assad and publish pro-Assad propaganda.
A $100,000 reward is being offered for information leading to their arrests and they're believed to be in Syria.
In April 2013, they allegedly sent a tweet from the Associated Press account on Twitter falsely claiming a bomb had exploded at the White House and injured the president. The message caused the stock market to dip significantly before the tweet was quickly determined to be a hoax.
They allegedly altered Harvard University's website home page, substituting an image of Syrian President Bashar al-Assad, with a message saying "Syrian Electronic Army were Here."
They are accused of creating a false online post on the Washington Post; unsuccessfully targeting members of the Executive Office of the President; defacing a blog and Twitter account belonging to Microsoft; sending false news tweets from Reuters' Twitter account and posting a false report on a journalist's blog; and posting messages on Human Rights Watch criticizing its own reports on Syria as "false."
Other media the two allegedly compromised in spear-phishing efforts include National Public Radio, CNN, The Onion, E! Online, the Daily Dot, New York Post, Time magazine and Vice. They also allegedly managed to take down the New York Times website after compromising its technology vendor.
Pierre Romar, 36, was also charged separately for his role in an extortion hacking scheme from 2013 through 2014. He was believed to be in Germany.
Romar allegedly was inspired by the hacking activities perpetrated by Agha and Dardar and wanted to join the Syrian Electronic Army, reaching out to Agha for help with a cyber attack he was planning against targets in Saudi Sauidi Arabia, Turkey and Qatar. According to the complaint, Agha connected him with Dardar on Facebook and the two worked together on an extortion scheme targeting U.S. and international computers and send victims threats to pay up after gaining access to their system through a spear-phishing attack.
Romar's location, in Germany, helped facilitate transferring the money to Syrian Electronic Army members in Syria because of U.S. sanctions.
John Carlin, the Justice Department's top national security attorney, said the allegations show the "increasingly blurry" line between criminal hackers and "potential national security threats."
Dardar allegedly demanded more than a total of $500,000 from 14 victims but ultimately accepted smaller amounts in many circumstances. Victims included an online gaming company, an online entertainment service, a Swiss web hosting provider, a United Kingdom-based web hosting company, a Europe-based web hosting company, a California-based web hosting company. In the last case, the company and some of its clients' Internet traffic was redirected to a site that said they had been hacked, alleged to have downloaded all their data and threatened to sell the databases for $100 to other hackers if it failed to comply.
The California-based company, which was not identified, ultimately paid about $1,500 to "Peter Romar in Germany" through Western Union after their bank denied the transfer to Syria — despite an initial demand of 105,000 euros.
The Associated Press contributed to this report.





