SUFFOLK, Va. — The massive coordinated cyber attack began with rolling blackouts throughout on the electrical grid stretching across the Midwestern United States, leaving up to 10 million Americans' homes without power and businesses unable to process credit and debit card purchases.
Then came the inexplicable malfunction at a large oil refinery in Port Arthur, Texas, which spewed an oil-slick five-miles wide along the gulf coast shoreline. The governors of Texas and Louisiana declared a states of emergency. In southern California, the cyber-attack shut down operations at several major ports by disabling the facilities' automated hydraulic systems. Dozens of cargo ships were stranded off the coast of Los Angeles, unable to offload their stacks of truck-sized containers.
Attacks on the Meanwhile U.S. Defense Department's networks threatened came under intense attack from an unknown enemy, threatening the software and satellite systems that monitor North American airspace and the radars on which the U.S. that military relies systems depend on.
Total mayhem.
This fictitious The catastrophic scenario was laid out for nearly 1,000 military, government and private sector personnel cyber security experts here at this year’s annual Cyber Guard exercise, the nation’s largest test of its network cyber defenses conducted by the military and civilian government agencies. Conducted Held over nine days in June on a military installation in Suffolk, Va., the event exercise offered a disturbing look at the type of catastrophe that what could unfold during the threats that today’s military cyber warriors and civilian tech experts might face in the event of what the government's top officials call warn could be a "cyber 9/11."
"For us, it's not a question of if it will happen but when," said Coast Guard Rear Adm. Kevin Lunday, U.S. Cyber Command's director of training. "The more relevant question is: When it does [happen], will we as a Department of Defense, will we as a nation and with our allies, be ready for it?"
While the Cyber Guard exercise is a classified event, Military Times was part of a small, select group of media granted rare access to the exercise's final day. Officials with the highly secretive CYBERCOM provided to a small group of reporters on June 17, the exercise’s final day, offering the Military Times and several other news organizations a tour of the facility, and interviews with participants and organizers.
This year’s exercise was focused on defensive cyber capabilities. The scenario involved an opposing force, referred to as a or "red team." The that was major nation state — though unnamed, it was most likely China or Russia — mounted ing an attack on the United States’ energy and transportation infrastructure. The scenario at last year’s exercise simulated an attack on major financial institutions.
About half of the participants were from CYBERCOM. The others included while the other half were civilians from the Department of Homeland Security, the FBI and other government agencies, and along with private sector officials from energy companies, major port facilities and privately owned internet service providers. The training network, built specifically for this exercise, replicates military and private-sector communications systems but is not connected to the internet. Training on an internet connection would risk releasing classified — or potentially even catastrophic — code-based weaponry into the public realm.

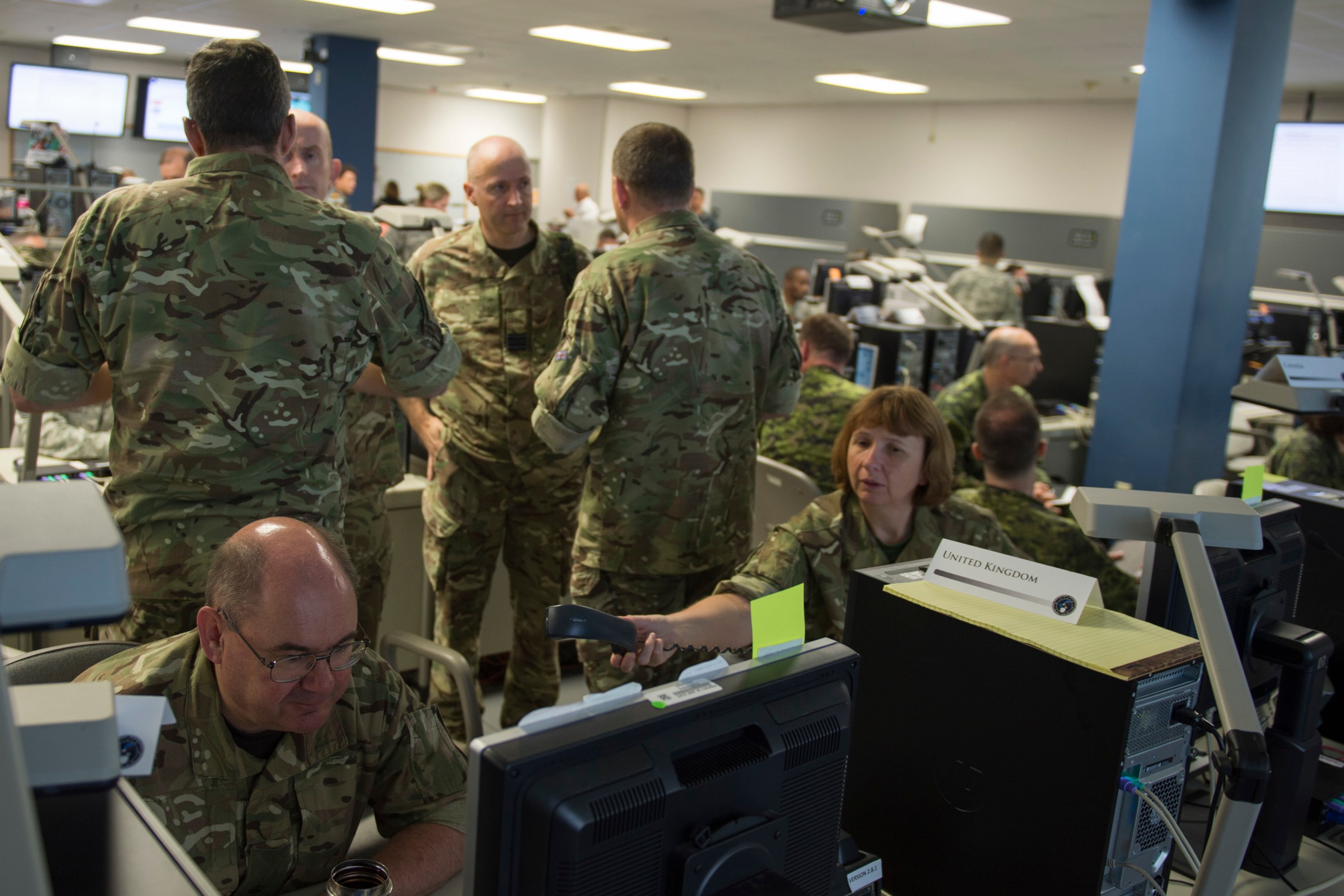
Cyber Guard participants huddle June 16, 2016, during a training scenario in Suffolk, Virginia.
Photo Credit: Petty Officer 2nd Class Jesse Hy/Navy
The 'White Cell'
The exercise was orchestrated from a "white cell" command post, where administrators direct the "red team" attacks and monitor the responses from the "blue teams" assigned to defend the American networks. The On the final day of the exercise, the "white cell" room bustled with military and civilian personnel officials, tapping on keyboards and monitoring large wall-mounted screens with maps and graphs illustrating the networks' flow of data through the networks.
"It’s not a rote script. It’s a series of injections," one of the exercise planners said. For example, maybe the oil spill gets really bad really quickly, the official said. Maybe the attack spreads to interstate highways by disabling gates, manipulating electronic traffic signals and creating havoc on the roadways, the official said.
At one point in the exercise, the personnel cyber warriors trying to fix the problem saw their keyboard converted into a foreign language script, rendering them unable to read the code they typed on the screen, one official said. The trainees suffered a lot of setbacks. But the point of the exercise is not a traditional competition between the Americans and the opposing forces.
"I’m often asked: ‘Who is winning?’ Lunday said. "But this is not a capture-the-flag scenario. It’s a classic military training exercise. We are assessing their capability to perform their mission-essential tasks. "The opposing force works for me, and" the training director said, "And I direct them to dial up the pressure to keep that training audience at the point of failure, where that learning is going to occur."
Noteworthy progress, but work remains
The For CYBERCOM, the exercise is a major milestone for CYBERCOM's its teams, of cyber professionals warriors who are striving for what the military calls "Full Operational Capability," or FOC status. Created in 2010, CYBERCOM is standing up a cyber-mission force of 6,200 active-duty specialists organized in 133 teams.
Progress has been slower than hoped, however. The target date for standing up those teams was initially set for the end of 2016, but that deadline has been pushed out to 2018. So far, about half of those teams have reached what's called "initial operational capability," and only 27 have reached "full operational capability," the final phase of readiness development.
CYBERCOM sent 24 teams to the Cyber Guard exercise in Virginia, each with about 30 to 40 personnel cyber warriors. All of those units have IOC status and are working toward FOC status.
CYBERCOM is still a relatively new organization, and military officials continue to are still hammering out the details for how to define and measure readiness. For now, the annual exercise is one of the cyber force’s primary opportunities to assess ccess the force’s capabilities.
"Cyber Guard is a pretty good example of where our force is at," said Maj. Gen. Paul Nakasone, commander of the CyberComs Cyber National Mission Force, which is the component that conducts offensive operations in cyber space. "Four years ago, we came here with soldiers, sailors, airman and Marines that were really focused on individual skills. ... Now four years later, we come with teams that are trained, ready to be certified, ready to be tested at a higher level."
In addition to the hundreds of troops at the main facility in Suffolk, the exercise was wired into several other locations where participants were working simultaneously on the same network. That included teams at Fort Meade in Maryland and a Department of Homeland Security team based in Pensacola, Fla.
The But the network used for the Cyber Guard exercise was temporary and will be dismantled when it's over afterward. That’s a concern for many top CYBERCOM's top officials, who have requested are penciling into their budgets millions of dollars to build a "persistent training environment" that will permanently link the military's cyber training facilities and make team-level activities a routine part of training.
"Here's our challenge," Nakasone said. "This is once a year. I need teams that can do this rapidly more than once a year."
Command-and-control: It's complicated
In one room, about 25 people from the Defense Department and the Federal Aviation Administration fought back an attack on the FAA’s networks that provide a vital stream of data used by the military to monitor and protect U.S. airspace. While the simulation simulated attack did not seek to shut down that FAA’s system, the malicious code, known as malware, was stealing vast amounts of data and sending it to an adversary with detailed visibility on the airspace over North American airspace.
In another room, one of a team of California reservists from California worked alongside the civilians who run the major ports of southern California's major ports. The reservists, activated by the governor of California's governor, were assigned to support the civilian efforts.

Adm. Michael S. Rogers, head of U.S. Cyber Command and the National Security Agency.
Photo Credit: Petty Officer 2nd Class Jesse Hy/Navy
Throughout the exercise, intelligence was relayed up and down the chain of command. Reservists working with port officials sent reports about the kind of malware they identified and evidence that might reveal who is behind the attack. At the same time, that team was receiving intelligence about the attack's source, specifically the web addresses — "URLs" — that will help block further infiltration.
In the real world, that would be a tricky legal situation. Like most of nation's major infrastructure, the ports — and their networks — are owned by private companies who must authorize any actions by the military's cyber force warriors. The military guard would have to provide "over-the-shoulder" support unless a detailed legal agreement was put into place that would allow for the military officials to work direct access to ly on the private network.
"A man filling sandbags to stop a flood is different from a man sitting down at a keyboard and looking at your network," said one reserve officer. "We might say ‘Hey, we need to put a block in the firewall.’ They approve it, and we do it." the reserve officer said.
In April the Government Accountability Office published a troubling report that said the Pentagon does not have a clear chain of command for responding to a massive cyber-attack, mainly due to policies that blur the lines between U.S. Northern Command and U.S. Cyber Command. One point of this exercise is start to start untangling this the knot of legal issues that would arise in the event of a major cyber-attack on the United States.
Some issues might fall under law enforcement jurisdiction, handled by the FBI. Others might appear to be acts of war that would fall under war-related authorities, require military support or involvement from the intelligence agencies. In some cases, military cyber specialists warriors would operate as a traditional active-duty force. In but in other cases, they might be reservists activated by state governors. In April the Government Accountability Office published a troubling report that said the Pentagon does not have a clear chain of command for responding to a massive cyber-attack, mainly due to policies that blur the lines between U.S. Northern Command and U.S. Cyber Command.
Several months before the Cyber Guard exercise, CYBERCOM hosted what's called a "tabletop exercise" that delved into many of these legal and policy issues, official said. Ultimately, they But those issues – that will be central to White House discussions about responding to a real cyber attack. However, they – were not a focus of this exercise.
"This is a tactical exercise," one CYBERCOM said CyberCom official said. "We’re not necessarily exercising the high-level command and control."
The Government Accountability Office says the Pentagon does not have a clear chain of command for responding to a massive cyber-attack.
Photo Credit: Petty Officer 2nd Class Jesse Hy/Navy
Andrew Tilghman is the executive editor for Military Times. He is a former Military Times Pentagon reporter and served as a Middle East correspondent for the Stars and Stripes. Before covering the military, he worked as a reporter for the Houston Chronicle in Texas, the Albany Times Union in New York and The Associated Press in Milwaukee.





