Hackers have gained access to sensitive data from at least five law firms in the past four months, releasing stolen data that includes pain diary entries from veterans’ personal injury cases, Emsisoft, a cybersecurity and anti-malware company, told Military Times.
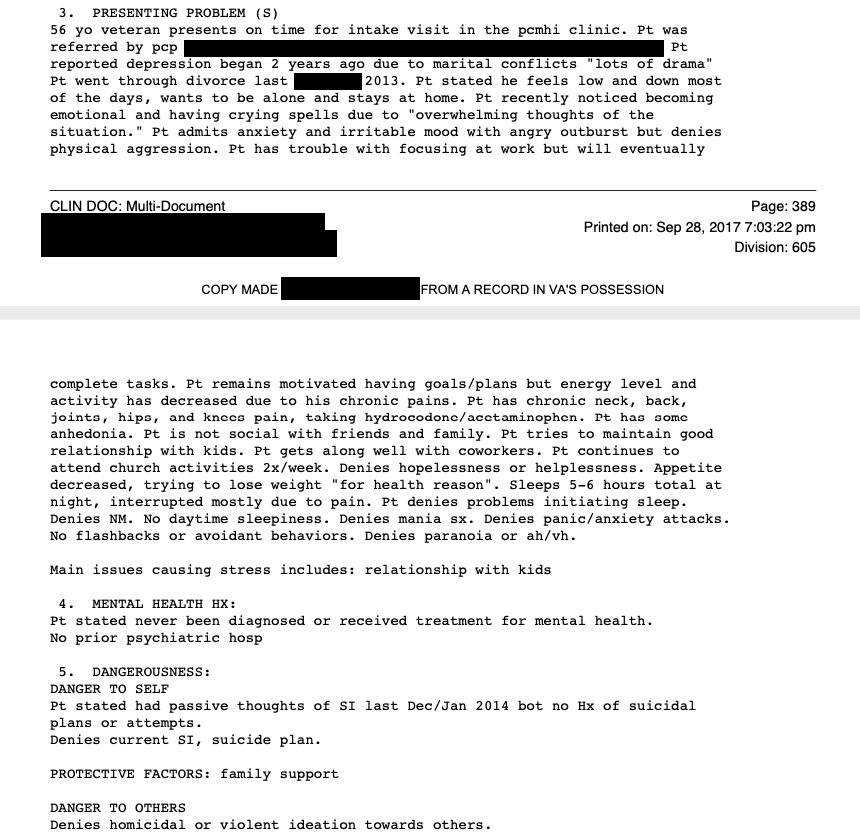
Maze, a hacking and ransomware group, has breached several law firms, local government databases and other companies, demanding payments for data recovery and deletion. The posted information includes VA documents, patient care records, legal fee agreements and privacy consent forms.
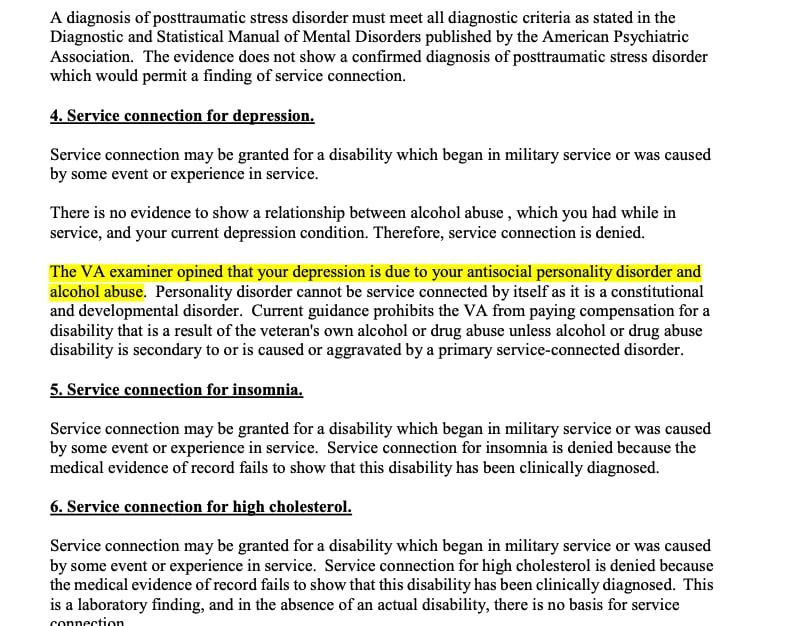
Two of those hacks targeted Texas-based law firm Baker Wotring in November and Woods and Woods LLC in Evansville, Indiana, this month, the Evansville Courier & Press reported.
Woods and Woods is a nationwide disability benefits firm that deals with U.S. Department of Veterans Affairs litigation.
“[Woods and Woods LLC] has notified the FBI and has taken and continues to take prompt action to contain the incident, mitigate its effects, and fully investigate,” said Neil Woods in an emailed statement to Military Times. “The firm is able to continue conducting its business since it had backups in place. The firm will provide additional information to its clients as the investigation continues.”
It is unclear, however, whether clients from the firms are aware some of their sensitive information has already posted to the web.
Baker Wotring did not respond to a request for comment.
Maze hacks an organization’s servers, notifies them of the breach and demands ransom payments to prevent data dumps, according to Brett Callow, a threat analyst with Emsisoft. If the group does not receive payment, it will publish small amounts of compromised data — “proofs” — online, accessible to anyone with internet access.
The group has previously demanded payments ranging from $1 million to several million dollars, and if payment is not received, Maze will release additional sensitive data on a staggered basis, Callow explained. Maze has already released a portion of personal documents from Woods and Woods, and the group claims to have more information.
Maze has also posted the compromised data to a Russian hacker forum, Callow said.
In some cases, other hackers will use the stolen information to target and demand ransom from individual patients or clients. Maze itself wrote on its site, “Use this information in any nefarious way that you want,” Callow said.
Ransomware and malware breaches have become devastated organizations in recent years, often crippling their ability to function or demands extraordinary sums of money.
A 2019 Emsisoft report found that 113 state and municipal governments and agencies, 764 health care providers, and 89 universities, colleges and school districts nationwide.
These groups prefer to target smaller firms with less secure cybersecurity infrastructure, Callow previously told Law.com. The Federal Bureau of Investigation (FBI) issued a Flash Alert last month to private companies to notify them of increased Maze ransomware activities, BleepingComputer reported.
Dylan Gresik is a reporting intern for Military Times through Northwestern University's Journalism Residency program.